Cara Copy Dongle Software Key
I have software that I have to have a usb dongle plugged in because it contains the key for it. I'm always weary of accidentally breaking it or it crapping out and not. Copy Dongle Usb Look at most relevant Cara copy security dongle usb websites out of 2.14 Million at MetricsKey. Cara copy security dongle usb found at softwaretopic. Cara copy dongle usb key cara cloning software usb dongle Cara Usb Dongle at Software Informer X-Micro Bluetooth USB Dongle 2 4.0.1.2101 Free This program allows a computer with a USB to communicate with other Bluetooth. Source: Forum Delphi Indonesia DonVall - 21:36 Post subject: Tanya: Menggunakan USB dongle untuk security software Halo semua.
Reversing aint easy these days and is getting harder. Every other executable is packed with this or that, PEID is no longer updated, and many software companies are moving towards dongle based security. The idea is simple – store the registration key or encryption key on a mobile piece of hardware.
So what is a dongle? Traditionally a dongle is a hardware device that connects to the PC through one of the ports in the back. The older ones used the parallel printer port.
- How to clone sentinel dongle USB keyDowload Link for Video: https://www.mediafire.com/folder/1x3jbe6et8cbe/.
- This is a virtual copy of your dongle. Download DongleBackup2012.zip, open it and unpack DongleBackup2012.exe to your computer, it can be your desktop or download folder for example. We strongly recommend downloading and saving Virtual Dongle Image (.DNG) file to the same folder.
- A software protection dongle (commonly known as a dongle or key) is an electronic copy protection and content protection device. When connected to a computer or other electronics, they unlock software functionality or decode content.
Finding a computer with a parallel port these days is tough, so as with all technology, adaptations were made. Now, USB is the defacto standard.
These are relatively cheap to produce and are hard to crack. The fact of the matter is, depending on how the dongle protection is incorporated, it can be impossible to crack a program without the device. Not completely impossible however. Like I said, if the protection is implemented wrong, it cracking the program could be as simple as a 3 byte patch of changing

cmp eax,0
jne 040032BE
RET
to
JMP 040032BE
There are 2 ways to implement a dongle. The right way and the wrong way. The right way would be to encrypt your programs and store the encryption key on the dongle and decrypt at run time depending on whether the device is connected or not.
The wrong way would be to merely check for the presence of the dongle. Why? Device drivers can be produced to emulate the functionality and visibility of any device including USB and parallel devices. Not only that, the check for a device can be patched, quite easily. There are a few companies out there that implement dongle based protections to software companies as a 3rd party service taking the hassle of implementing a copy based protection system out of the hands of the software company. Trouble is, once you’ve cracked this 3rd party providor’s method, it works on EVERY ONE of their clients.
Take Sentinel from SafeNet for example: http://www.safenet-inc.com/support-downloads/sentinel-drivers/ . Their protection suite is quite popular, however recent versions produced have one fatal flaw – implementation of their dongle based copy protection can be halted based on a single 3 byte patch.
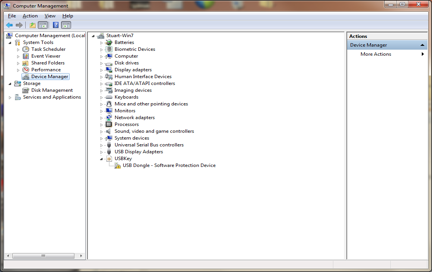
Say for example the software in question is done the right way – encrypted and needs the key to be decrypted at run time. How might this be cracked? Well for starters, we would need to identify the key. The key can be obtained either in memory during live analysis in a debugger or statically by probing the driver or contents of the USB device. Device drivers need to be debugged using a kernel debugger since drivers dont operate in user mode. WinDBG is suitable for this, however softice can be used as well. I myself have never been able to get softice working, but if you can, go for it. Another method would be to use this little program called USBSnoop – http://sourceforge.net/projects/usbsnoop/. This awesome tool allows for a tool that logs the usb data exchange between hardware and device driver. I’ve had excellent luck with this and have found the decryption key in plain text by analyzing the data stream log.

Once the key has been obtained, decryption of the program is possible. What would need to be done from there? One would need to either A) dump the decrypted program which would no longer need the key (depends on how the encryption is implemented) or create an emulator. The emulator would simply be a dummy USB device that contained a copy of the USB dongle – key and all.
Its hard to explain without going into full detail on how to create such an emulator, but guides do exist on how to create drivers. First off you’ll need the driver development kit from microsoft. Next, check out lib-usb from sourceforge: http://sourceforge.net/apps/trac/libusb-win32/wiki . Create a USB device driver that simulates the key or files being present on the newly emulated device. Maybe one day I’ll write a step by step on writing such a program, but for now however, we have the basics and concepts out of the way.
Copy Dongle Key
Expect more updates in the future.